إدارة التهديدات الأمنية
من الدفاع السلبي إلى اليقظة الفاعلة
التحول الرقمي يفتح آفاقًا لا حدود لها، لكنه يجلب معه مخاطر جديدة تتطلب اليقظة والسيطرة. في سيمافور كونسيل، نؤمن أن نموّكم يجب أن يكون قوة، لا عبئًا.
إدارة التهديدات الأمنية هي شريككم الذكي لمراقبة المخاطر الرقمية، تمكينكم من التحكم الكامل وحماية أعمالكم، مع إطلاق كامل إمكاناتكم الرقمية.
حلّنا الذكي لمراقبة المخاطر الرقمية
يوفّر التحول الرقمي فرصًا هائلة، لكنه يعرّض مؤسستكم أيضًا لمخاطر متزايدة. في سيمافور كونسيل، نؤمن بأن نموّكم لا يجب أن يكون عبئًا، بل رافعة للنجاح والتميز.
إدارة التهديدات الأمنية هي حلّنا الذكي لمراقبة المخاطر الرقمية، تمكّنكم من السيطرة الكاملة على التهديدات مع إطلاق كامل إمكاناتكم الرقمية.
OPSEC: من الفلسفة إلى التنفيذ

تحديد البيانات الحساسة
نحدّد أهم المعلومات والموارد الحيوية لشركتكم، لضمان أن تحظى بحماية أولوية قصوى.

تحليل بيئة التهديدات
نقوم بدراسة المنافسين والتهديدات المحتملة وأساليبهم، لتحديد من يمكنه استهداف أصولكم ولماذا.

تقييم الثغرات والضعف
نبحث باستمرار عن نقاط الضعف في دفاعاتكم، سواء كانت بشرية أو تقنية، لضمان عدم ترك أي ثغرة مفتوحة.

تقييم المخاطر
نقيّم احتمالية وتأثير التهديدات المحتملة، مما يتيح تخصيص الموارد الأمنية بكفاءة وفعالية عالية.

تنفيذ الإجراءات المضادة
نطبّق إجراءات استباقية ومحددة لتقليل المخاطر، وضمان حماية ومرونة عملياتكم التشغيلية.
تقديم الخدمات المدارة
(Managed Services)
في Semafor Conseil، يجمع نهجنا في تقديم الخدمات المدارة بين صرامة إدارة المشاريع الموجهة بمعايير معهد إدارة المشاريع (PMI)، ودورة الحياة التشغيلية (PDIO): (تخطيط – تصميم – تنفيذ – تشغيل). نهدف من خلال ذلك إلى ضمان تقديم خدمات تكنولوجيا معلومات موثوقة، متوقعة، ومتوافقة تماماً مع أهداف أعمالكم.
منظومة خدمات مهيكلة وآمنة
إطار عمل احترافي: خدمات محكومة باتفاقيات مستوى خدمة (SLA) واضحة، ومؤشرات أداء (KPIs) قابلة للقياس، وآليات حوكمة أثبتت كفاءتها.
استمرارية شاملة (منهجية PDIO)
إدارة كاملة للمشاريع تبدأ من مراحل التخطيط والتصميم، وصولاً إلى التنفيذ والتشغيل اليومي المستمر.
إحكام السيطرة على التكاليف والجداول الزمنية
انضباط عالٍ في إدارة المشاريع يضمن الوفاء بالالتزامات، مع توفير رؤية كاملة ورقابة دقيقة على كافة مراحل التنفيذ.
ذكاء تشغيلي متطور
لحماية أصولكم الرقمية
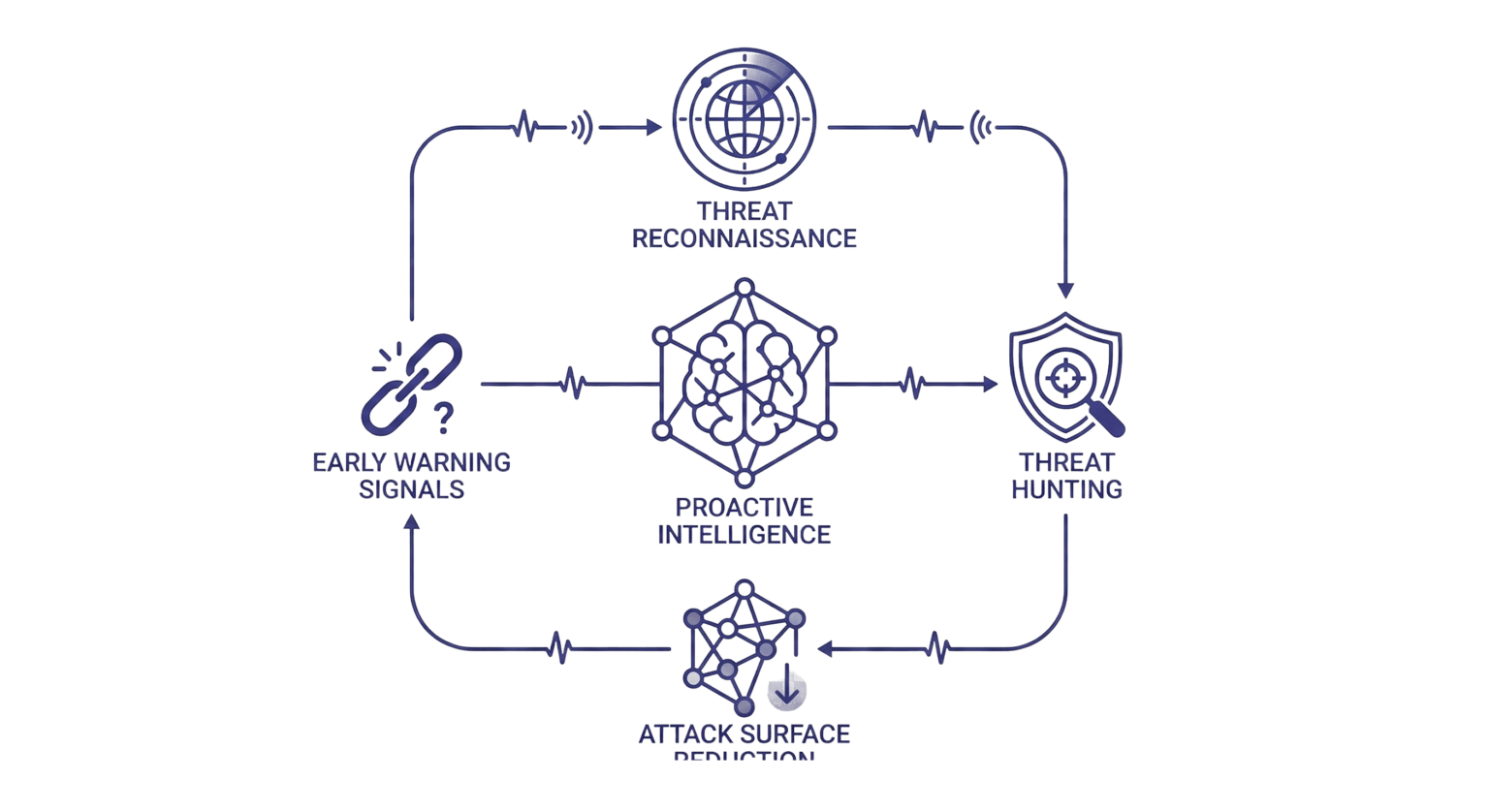
رصد استباقي للتهديدات
تحليل مستمر لتكتيكات المهاجمين وأحدث مؤشرات الاختراق لتمكينكم من التنبؤ بالمخاطر وحماية الأصول الحيوية قبل وقوع الهجوم.
تحليل SIEM في الوقت الفعلي
ربط ذكي لسجلات الأحداث ونظام الإنذار المبكر للكشف عن الإشارات الخفية والاستجابة بسرعة البرق قبل أي تهديد فعلي.
تقليل سطح الهجوم
إجراء تدقيقات مستمرة لتحديد الثغرات ومعالجتها قبل أن يتمكن أي مخترق من استغلالها.
الدرع الرقمي: دفاع متقدم


