SECURITY ONION
Your Open-Source Security Command Center
Turn security insights into real defensive action.
OVERVIEW
Security Onion: Your Open-Source Security Command Center
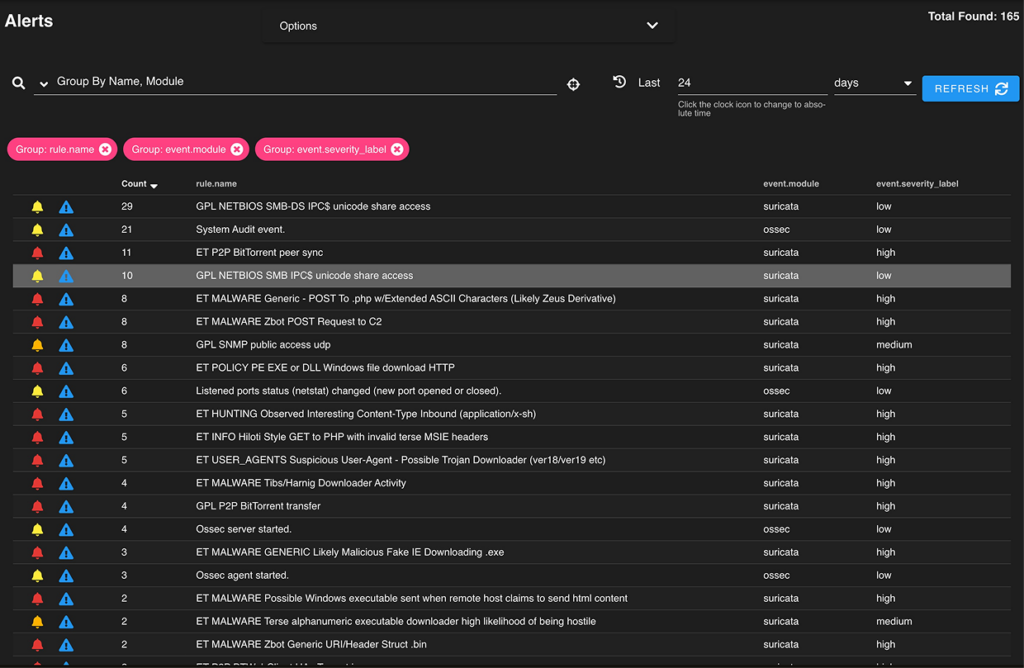
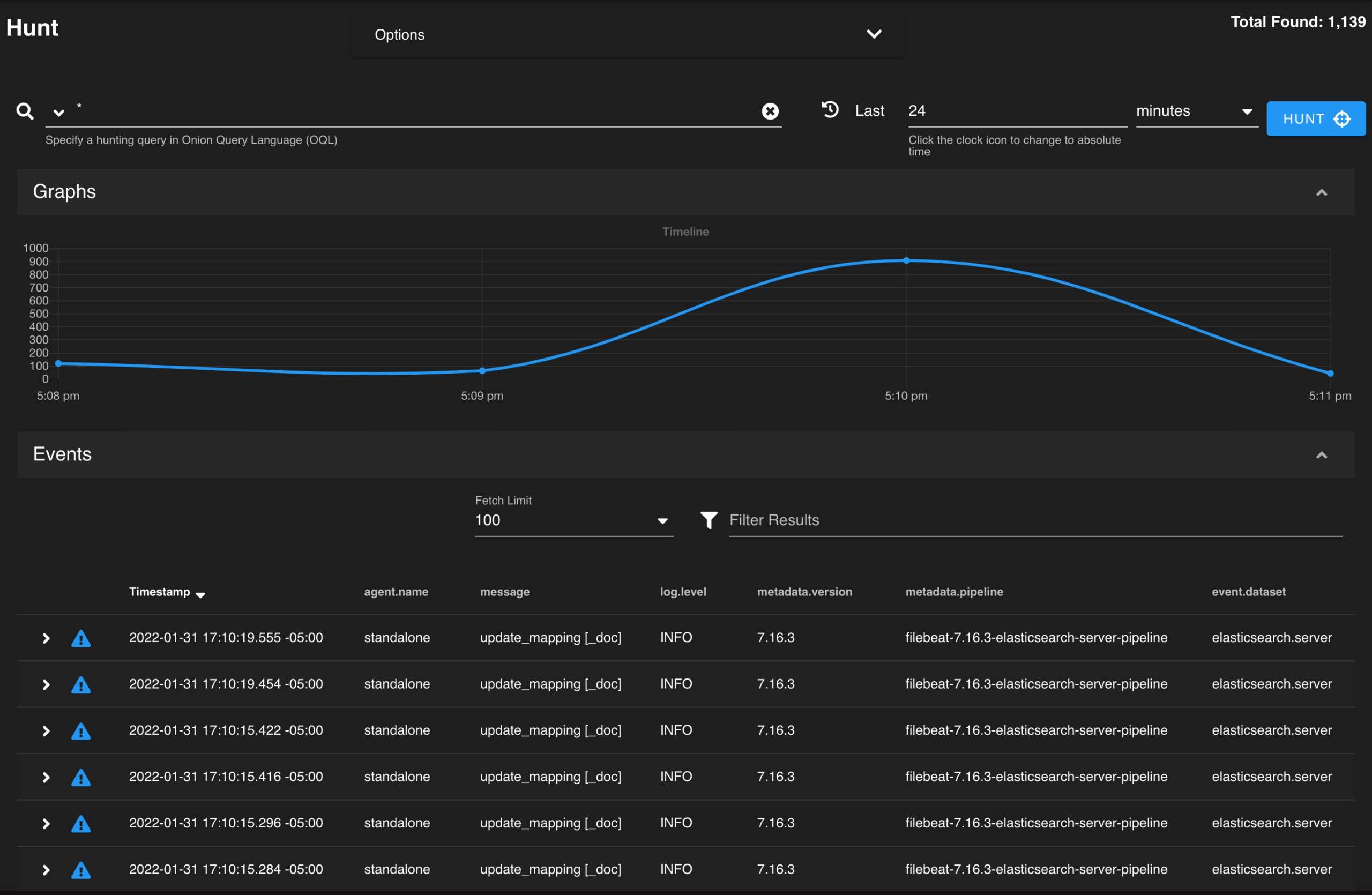
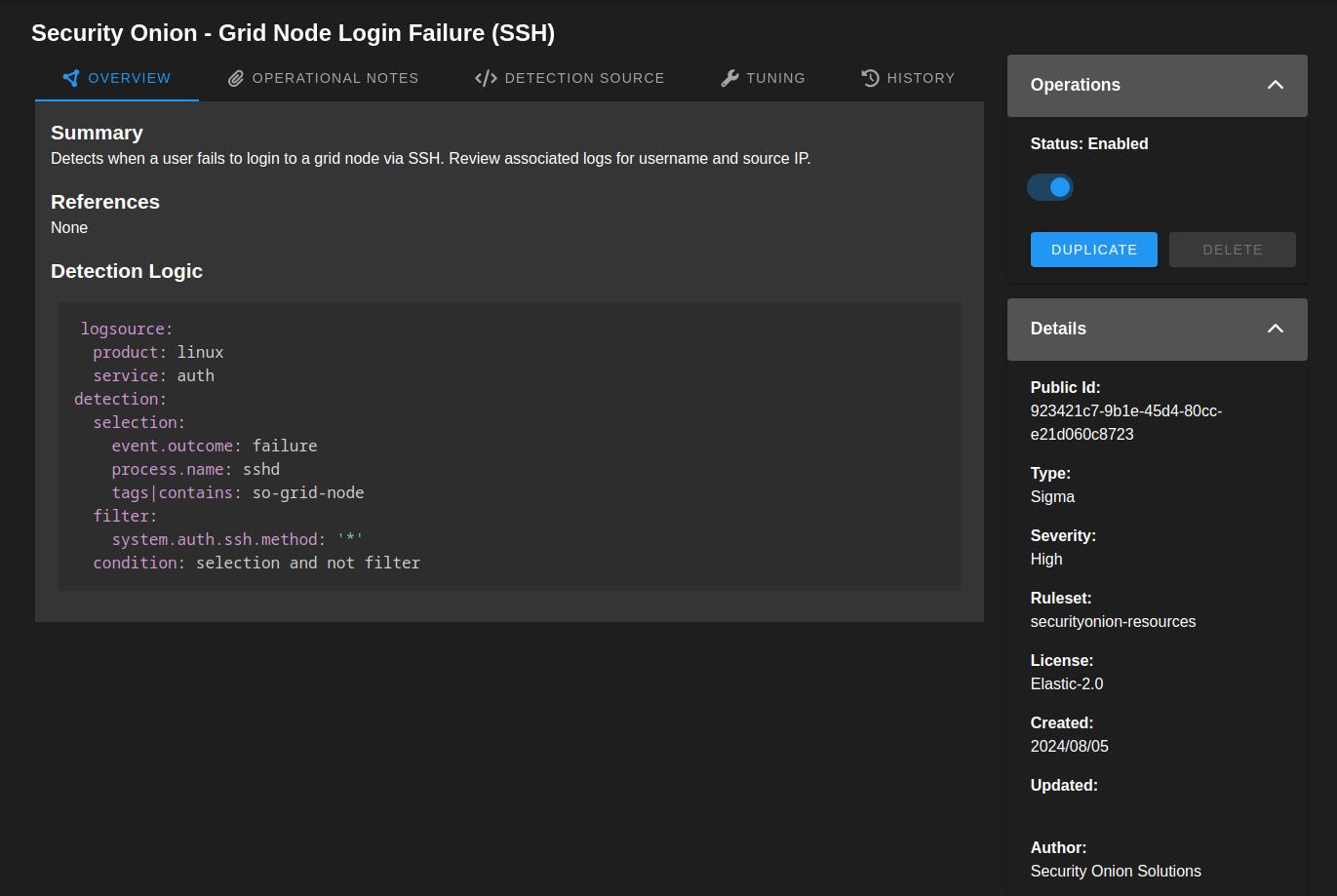
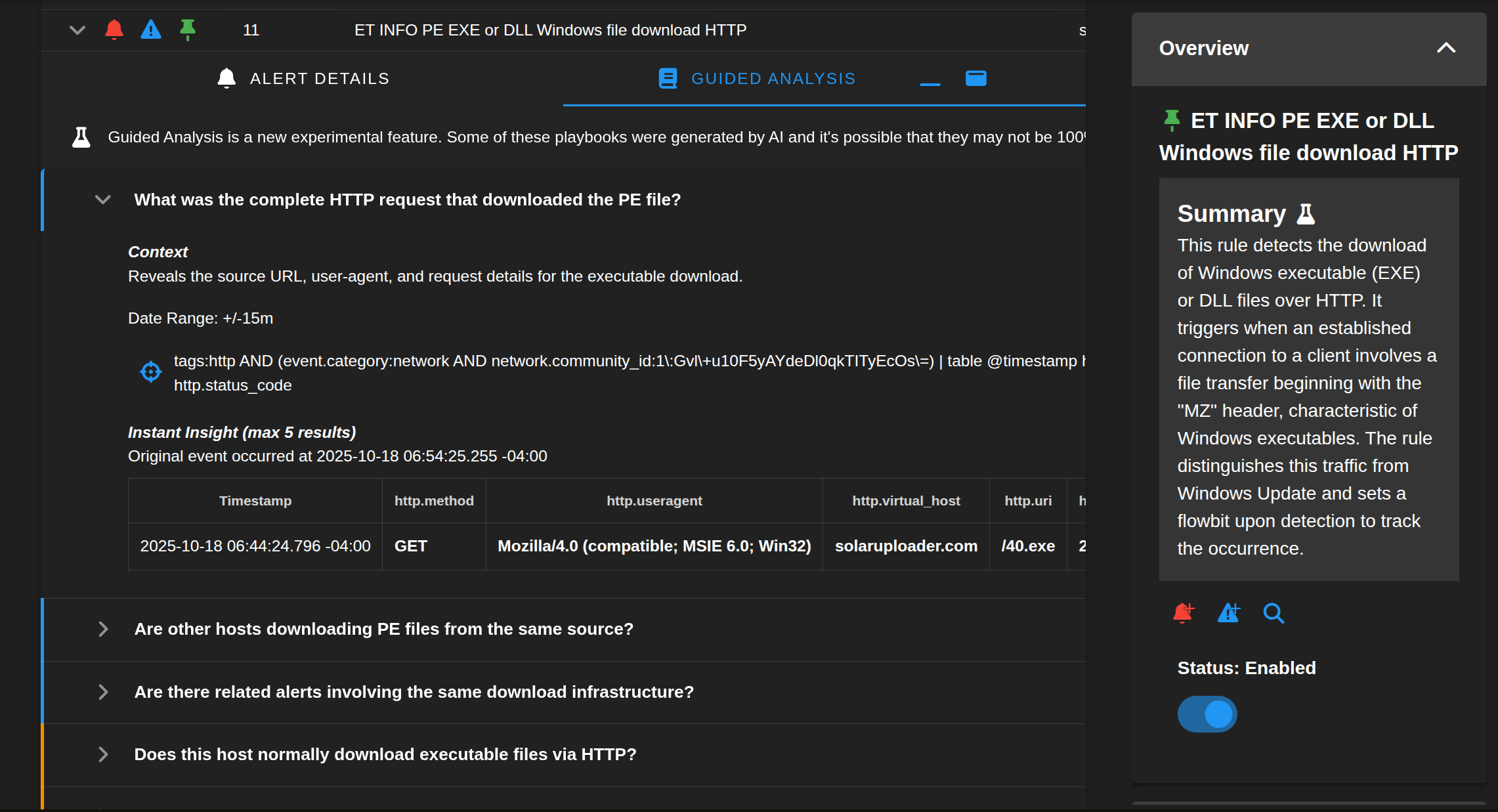
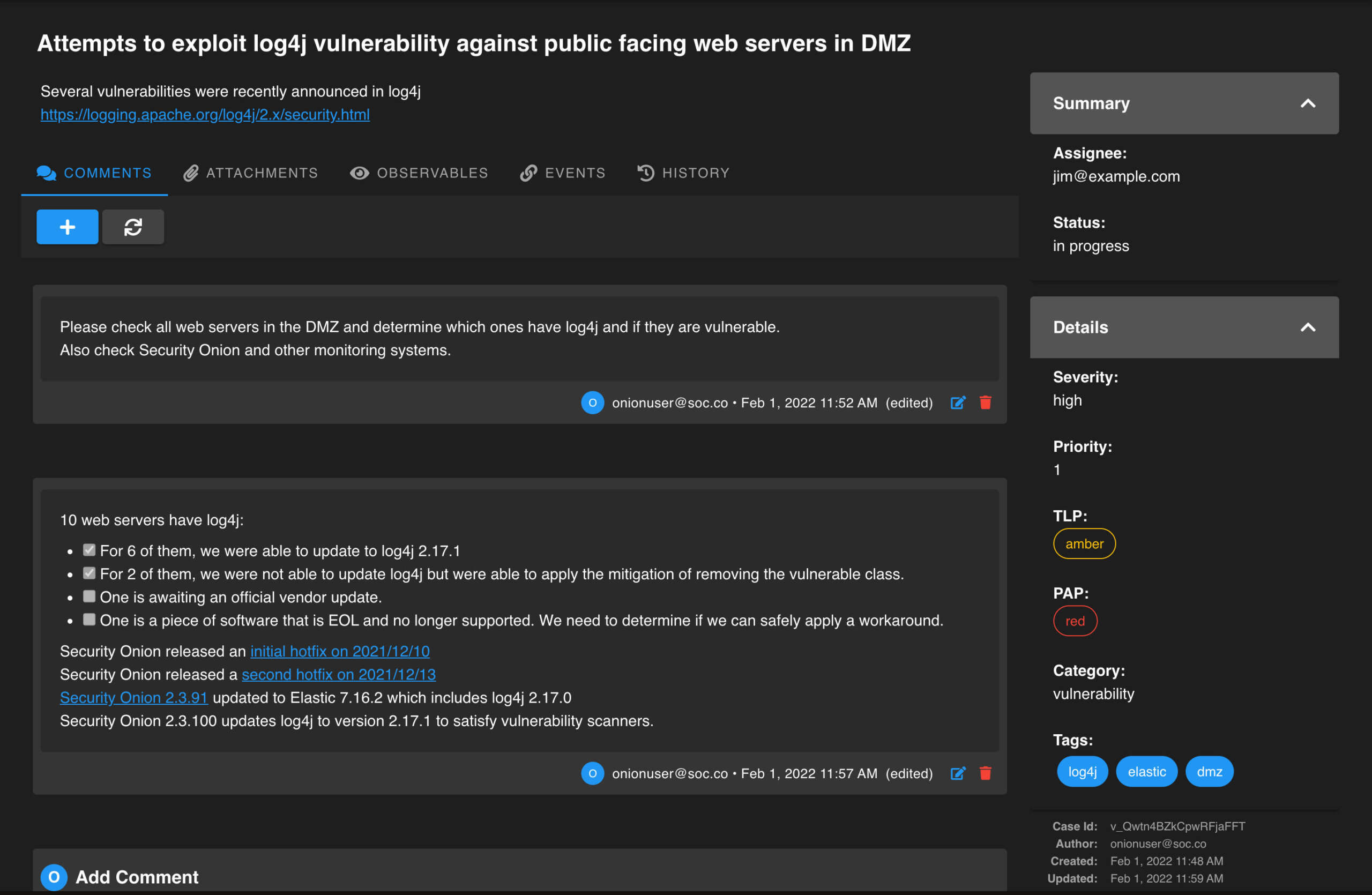
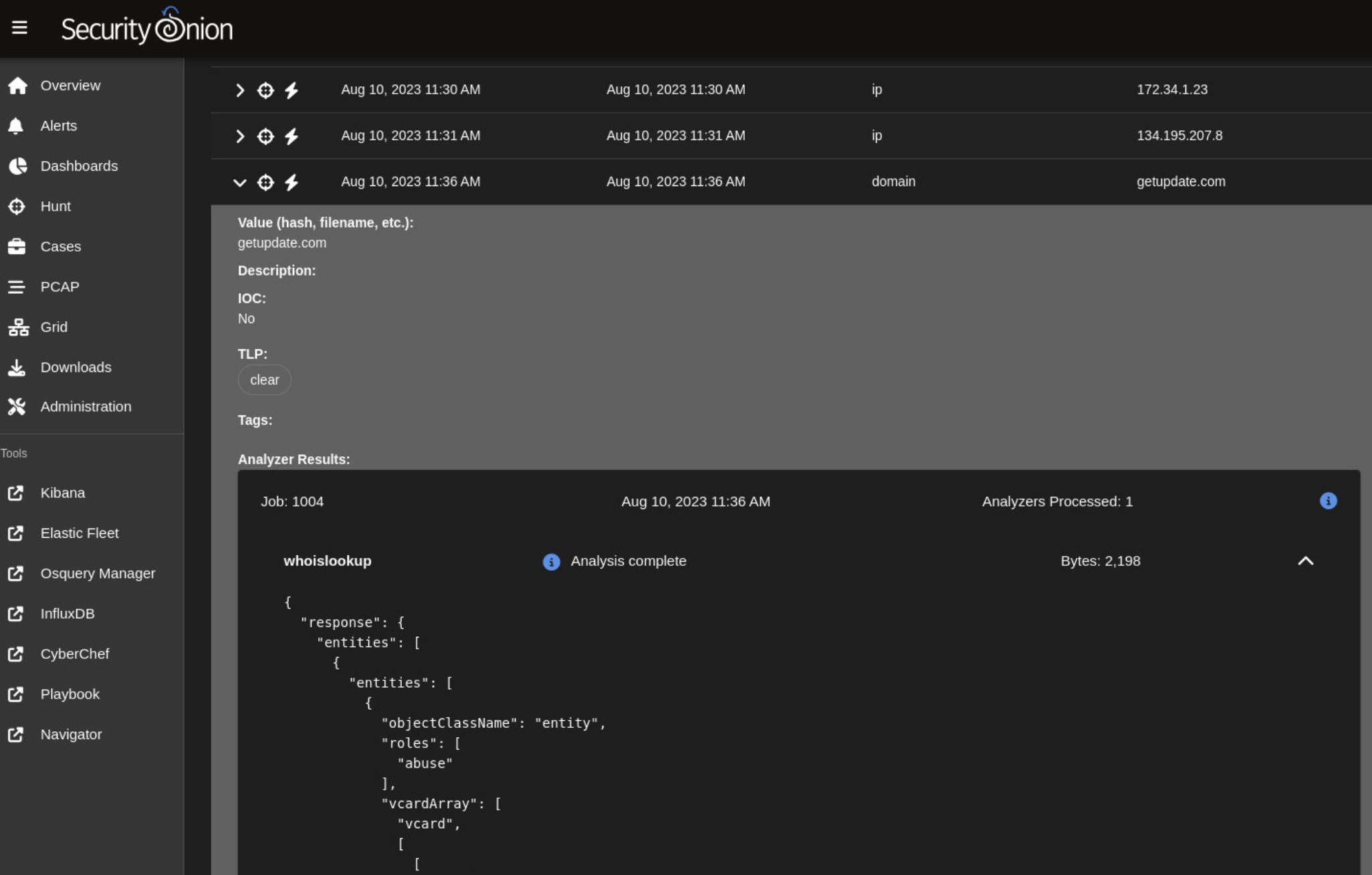
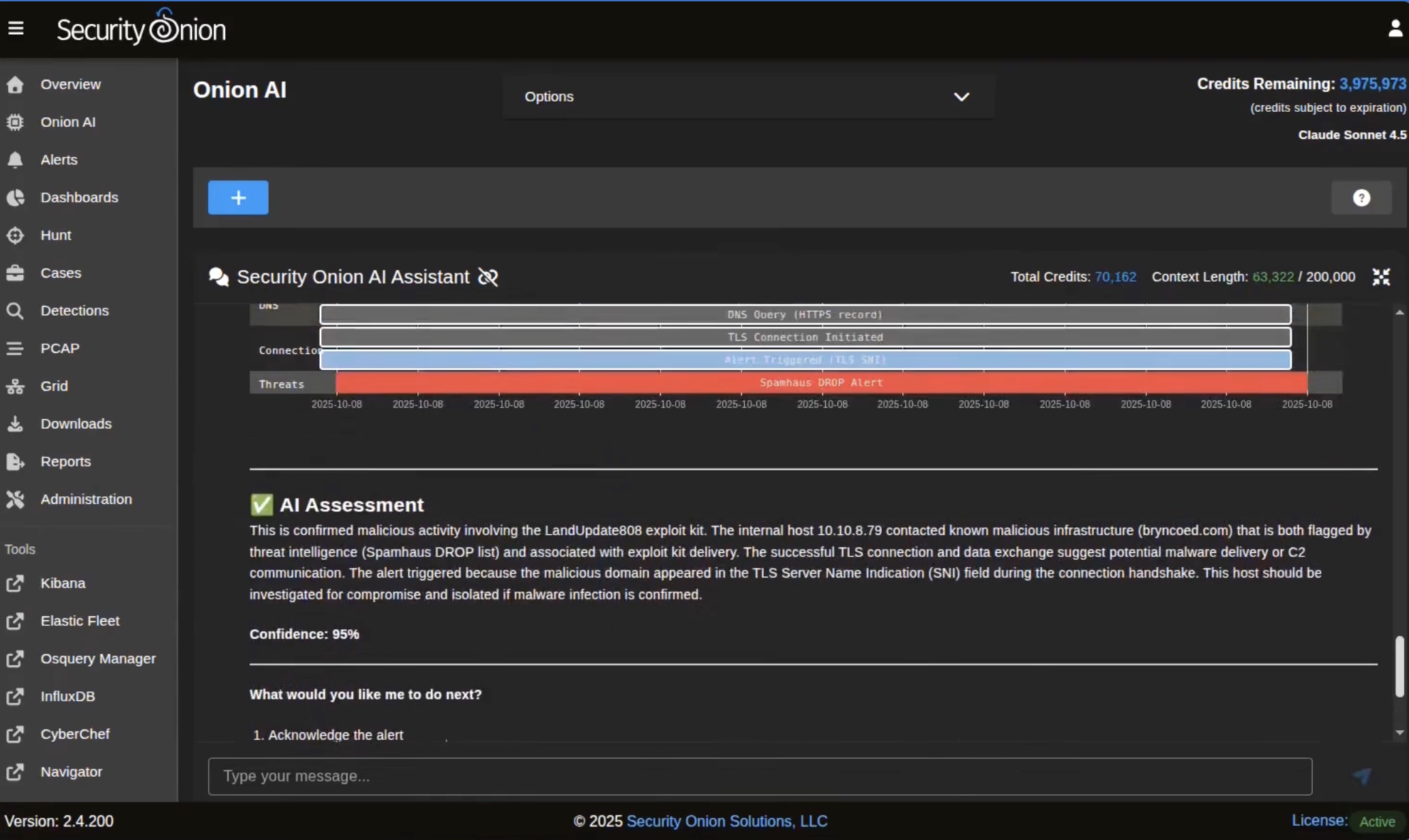
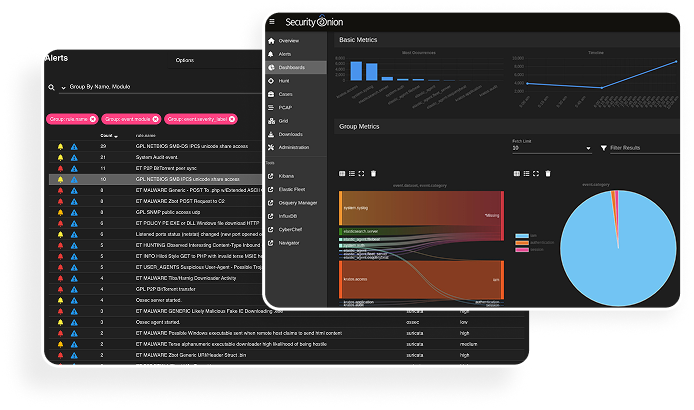
Security Onion is an open-source platform built by defenders, for defenders. It provides network visibility, host visibility, intrusion-detection honeypots, and centralized log and incident management.
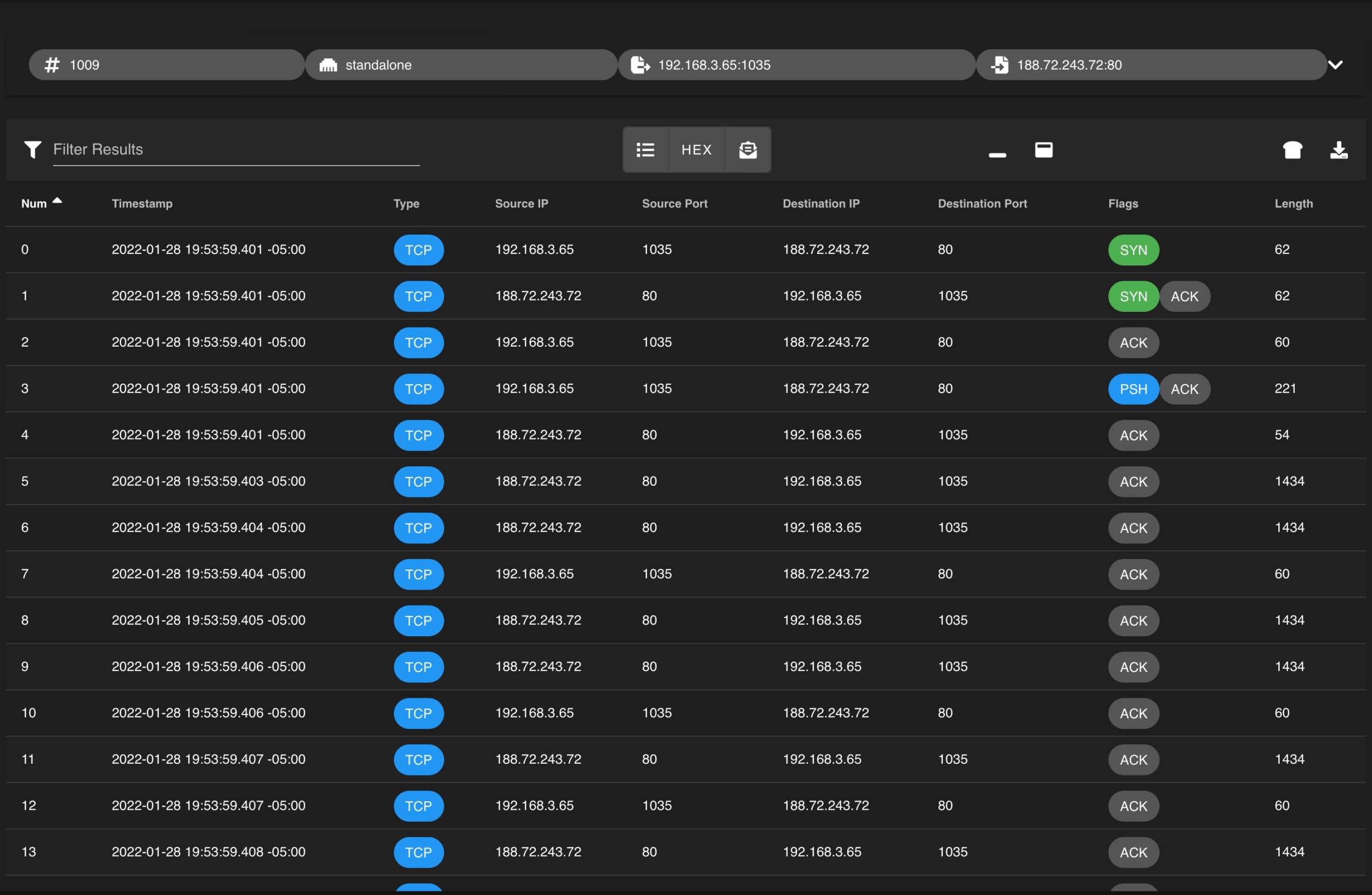
For network visibility, it offers signature-based detection via Suricata, rich protocol metadata, selective file extraction using Zeek or Suricata, full packet capture via Stenographer, and file analysis through Strelka.
For host visibility, Security Onion integrates the Elastic Agent for data collection, real-time querying via osquery, and centralized management through Elastic Fleet.
With over 2 million downloads, Security Onion is trusted by security teams worldwide to monitor and defend their infrastructures. Its intuitive setup assistant allows you to deploy a distributed grid for your organization in just a few minutes!
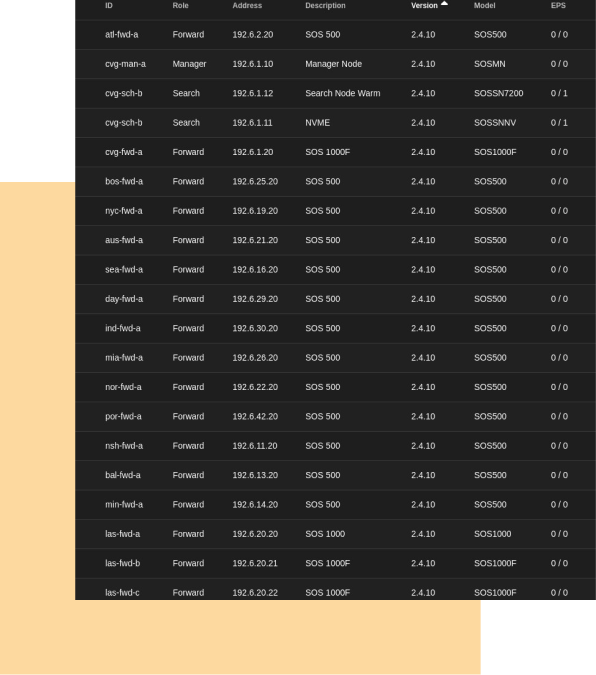
Highly Scalable
From a single network appliance to a thousand-node grid, Security Onion adapts to your specific needs.

Open Community
Security Onion and the tools we integrate are fully open-source and developed by the cybersecurity community.
The source code is available on GitHub, allowing anyone who wants to understand the system’s inner workings to examine it in detail.
Use Cases
01.
Network Visibility
Collect network events from Zeek, Suricata, and other tools for full network coverage. Deploy a wide net to quickly and easily detect malicious actors.
02.
Host Visibility
Collect host events from Zeek, Suricata, and other tools to achieve complete infrastructure coverage. Deploy a wide net to rapidly and efficiently identify malicious activity.
03.
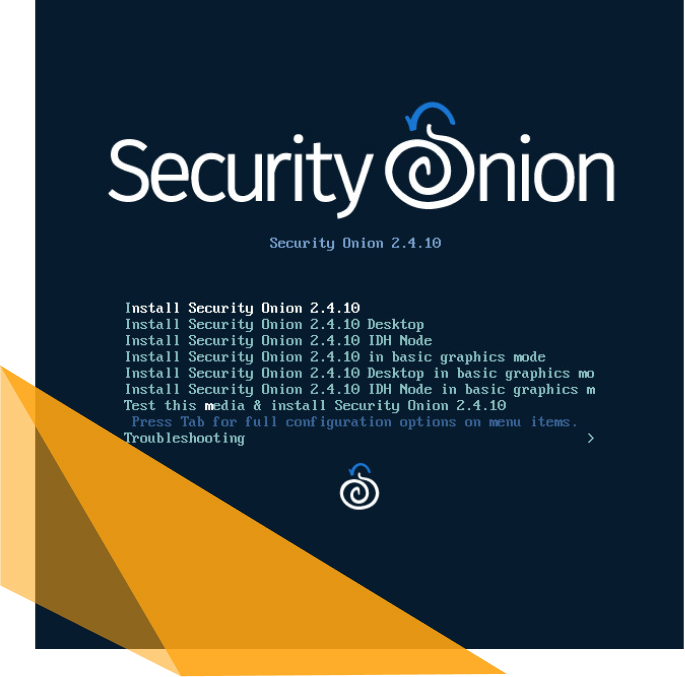
Static Analysis (PCAP & EVTX Import)
Analyze captured data with PCAP and EVTX files to gain deep insights into network and host activity. Quickly detect threats and understand their impact.
04.
Security Onion
Desktop
Collect network events via Zeek, Suricata, and other tools for comprehensive infrastructure monitoring. Deploy a wide net to detect malicious actors swiftly and effectively.